Discover The Best Remote SSH IoT Firewall Free Solutions For Enhanced Security
When it comes to managing IoT devices remotely, security is a top priority. The best remote SSH IoT firewall free solutions offer a seamless way to protect your devices while ensuring uninterrupted access. With the increasing number of IoT devices in homes and businesses, the need for robust security measures has never been greater. Remote SSH access provides a secure way to manage these devices, but pairing it with a reliable firewall is crucial to safeguard against potential threats. Whether you're a tech enthusiast or a business owner, finding the right combination of tools can make all the difference in securing your IoT ecosystem.
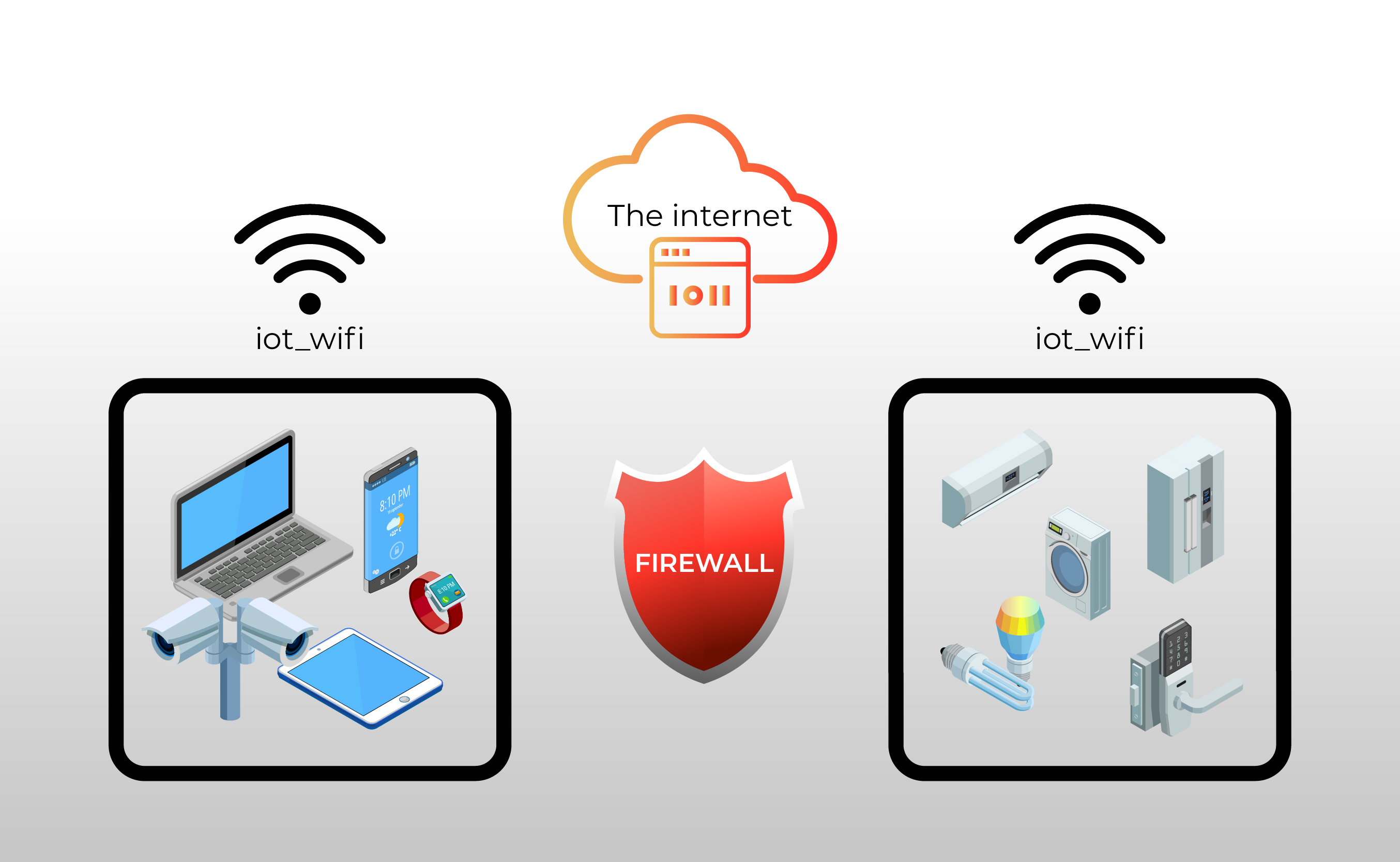
IoT devices are often vulnerable to cyberattacks due to their limited processing power and lack of built-in security features. This is where SSH (Secure Shell) and firewalls come into play. SSH allows you to securely connect to your devices over an encrypted connection, while a firewall acts as a barrier to block unauthorized access. Together, they form a powerful duo that can significantly enhance the security of your IoT network. But how do you choose the best remote SSH IoT firewall free tools? This article will guide you through the process and provide valuable insights to help you make an informed decision.
With so many options available, it can be overwhelming to find the perfect solution for your needs. That's why we've compiled a comprehensive guide to help you navigate the world of remote SSH and IoT firewalls. From understanding the basics to exploring advanced features, we'll cover everything you need to know to secure your devices effectively. By the end of this article, you'll have a clear understanding of the best remote SSH IoT firewall free options and how to implement them in your setup.
Read also:Discovering Stephen Walters The Journey Of A Remarkable Personality
- What is SSH and Why is it Important for IoT Security?
- How to Choose the Best Remote SSH IoT Firewall Free Solution?
- Top Features to Look for in a Remote SSH Firewall
- Can a Free Firewall Really Protect Your IoT Devices?
- Step-by-Step Guide to Setting Up SSH for IoT Devices
- What are the Common Threats to IoT Security?
- Best Practices for Securing Your IoT Network
- How to Test the Effectiveness of Your Remote SSH IoT Firewall?
- Why is Open Source Software a Good Option for IoT Security?
- Conclusion: The Future of IoT Security
What is SSH and Why is it Important for IoT Security?
SSH, or Secure Shell, is a cryptographic network protocol that allows secure communication between two devices over an unsecured network. It is widely used for remote administration of servers and IoT devices. SSH encrypts the data transmitted between devices, making it difficult for attackers to intercept and decipher sensitive information. This is particularly important for IoT devices, which often lack robust security features.
IoT devices are increasingly becoming targets for cybercriminals due to their widespread use and often inadequate security measures. SSH provides a secure way to manage these devices remotely, reducing the risk of unauthorized access. By using SSH, you can ensure that only authorized users can access your IoT devices, protecting them from potential threats.
How to Choose the Best Remote SSH IoT Firewall Free Solution?
Choosing the best remote SSH IoT firewall free solution requires careful consideration of several factors. First, you need to evaluate the features offered by the firewall. Does it provide the level of protection you need for your IoT devices? Is it compatible with your existing setup? These are important questions to ask before making a decision.
Another crucial factor is ease of use. A firewall that is difficult to configure and manage can be more of a burden than a benefit. Look for solutions that offer a user-friendly interface and clear documentation. Additionally, consider the reputation of the provider. Are they known for delivering reliable and secure products? Reading reviews and seeking recommendations can help you make an informed choice.
Can a Free Firewall Really Protect Your IoT Devices?
Many people wonder if a free firewall can provide adequate protection for their IoT devices. The answer depends on the specific firewall and its features. Some free firewalls are highly effective and offer robust protection, while others may lack essential features or have limitations. It's important to thoroughly research and test any free firewall before relying on it for your IoT security needs.
One advantage of free firewalls is that they often come with active communities and regular updates. This means that vulnerabilities are quickly addressed, and new features are added over time. However, it's crucial to ensure that the firewall you choose is actively maintained and supported. A neglected or outdated firewall can leave your devices vulnerable to attacks.
Read also:Czech Wife Swap Site Exploring The Culture And Community
Top Features to Look for in a Remote SSH Firewall
When evaluating remote SSH firewalls, there are several key features to consider. These features can significantly impact the effectiveness of the firewall in protecting your IoT devices.
- Encryption: Ensure that the firewall uses strong encryption protocols to protect data transmitted between devices.
- Access Control: Look for firewalls that offer granular access control, allowing you to specify which users and devices can access your network.
- Intrusion Detection: A good firewall should have intrusion detection capabilities to identify and block suspicious activity.
- Logging and Monitoring: The ability to log and monitor network activity is essential for identifying potential security threats.
- Compatibility: Ensure that the firewall is compatible with your IoT devices and operating systems.
Step-by-Step Guide to Setting Up SSH for IoT Devices
Setting up SSH for your IoT devices is a straightforward process, but it requires attention to detail to ensure security. Follow these steps to get started:
- Install SSH Server: Begin by installing an SSH server on your IoT device. Most Linux-based devices come with SSH pre-installed, but you may need to enable it.
- Generate SSH Keys: Create a pair of SSH keys (public and private) to authenticate your connection. This eliminates the need for passwords, which can be vulnerable to brute-force attacks.
- Configure Firewall Rules: Set up firewall rules to allow SSH traffic only from trusted IP addresses. This adds an extra layer of security.
- Test the Connection: Once everything is set up, test the SSH connection to ensure it's working correctly.
- Monitor and Update: Regularly monitor your SSH logs and update your firewall rules as needed to maintain security.
What are the Common Threats to IoT Security?
IoT devices are susceptible to a variety of security threats. Understanding these threats is the first step in protecting your devices. Some common threats include:
- Unauthorized Access: Attackers may attempt to gain unauthorized access to your IoT devices to steal data or disrupt operations.
- Malware: IoT devices can be infected with malware, which can compromise their functionality and security.
- Man-in-the-Middle Attacks: These attacks intercept and alter communication between devices, potentially leading to data breaches.
- DDoS Attacks: Distributed Denial of Service (DDoS) attacks can overwhelm your devices, causing them to become unresponsive.
Best Practices for Securing Your IoT Network
To enhance the security of your IoT network, consider implementing the following best practices:
- Use Strong Passwords: Ensure that all devices and accounts are protected with strong, unique passwords.
- Enable Two-Factor Authentication: Adding an extra layer of security can significantly reduce the risk of unauthorized access.
- Keep Software Updated: Regularly update your devices and firewall software to patch vulnerabilities and improve security.
- Segment Your Network: Use network segmentation to isolate IoT devices from critical systems, reducing the risk of widespread attacks.
How to Test the Effectiveness of Your Remote SSH IoT Firewall?
Testing the effectiveness of your remote SSH IoT firewall is crucial to ensure it's providing the level of protection you need. Here are some steps to follow:
- Perform Vulnerability Scans: Use tools to scan your network for vulnerabilities and address any issues that are identified.
- Conduct Penetration Testing: Simulate attacks on your network to identify weaknesses and improve your defenses.
- Monitor Logs: Regularly review firewall logs to detect any suspicious activity or potential breaches.
- Update and Patch: Ensure that your firewall and IoT devices are up-to-date with the latest security patches.
Why is Open Source Software a Good Option for IoT Security?
Open source software is often a great choice for IoT security due to its transparency and flexibility. With open source solutions, you can review the code to ensure there are no hidden vulnerabilities or backdoors. Additionally, open source communities are typically active and responsive, providing regular updates and support.
Another advantage of open source software is its cost-effectiveness. Many high-quality firewalls and SSH tools are available for free, making them accessible to individuals and businesses with limited budgets. By leveraging open source solutions, you can achieve robust security without breaking the bank.
Conclusion: The Future of IoT Security
As IoT devices continue to proliferate, the need for robust security measures becomes increasingly important. The best remote SSH IoT firewall free solutions offer a powerful way to protect your devices while ensuring secure remote access. By understanding the features and capabilities of these tools, you can make informed decisions to safeguard your IoT network.
With the right combination of SSH and firewall technologies, you can significantly enhance the security of your IoT devices. Whether you're a tech enthusiast or a business owner, investing in reliable security measures is essential to protect your devices and data. By following the best practices outlined in this article, you can create a secure and resilient IoT ecosystem that meets your needs.
Funny Fucked Up Jokes That Will Leave You Laughing And Thinking
Scarlett Johansson Height And Weight: A Comprehensive Guide To Her Physical Stats
Max Minghella Girlfriend: A Deep Dive Into His Love Life And Career
Firewall For IoT Devices The Ultimate Guide
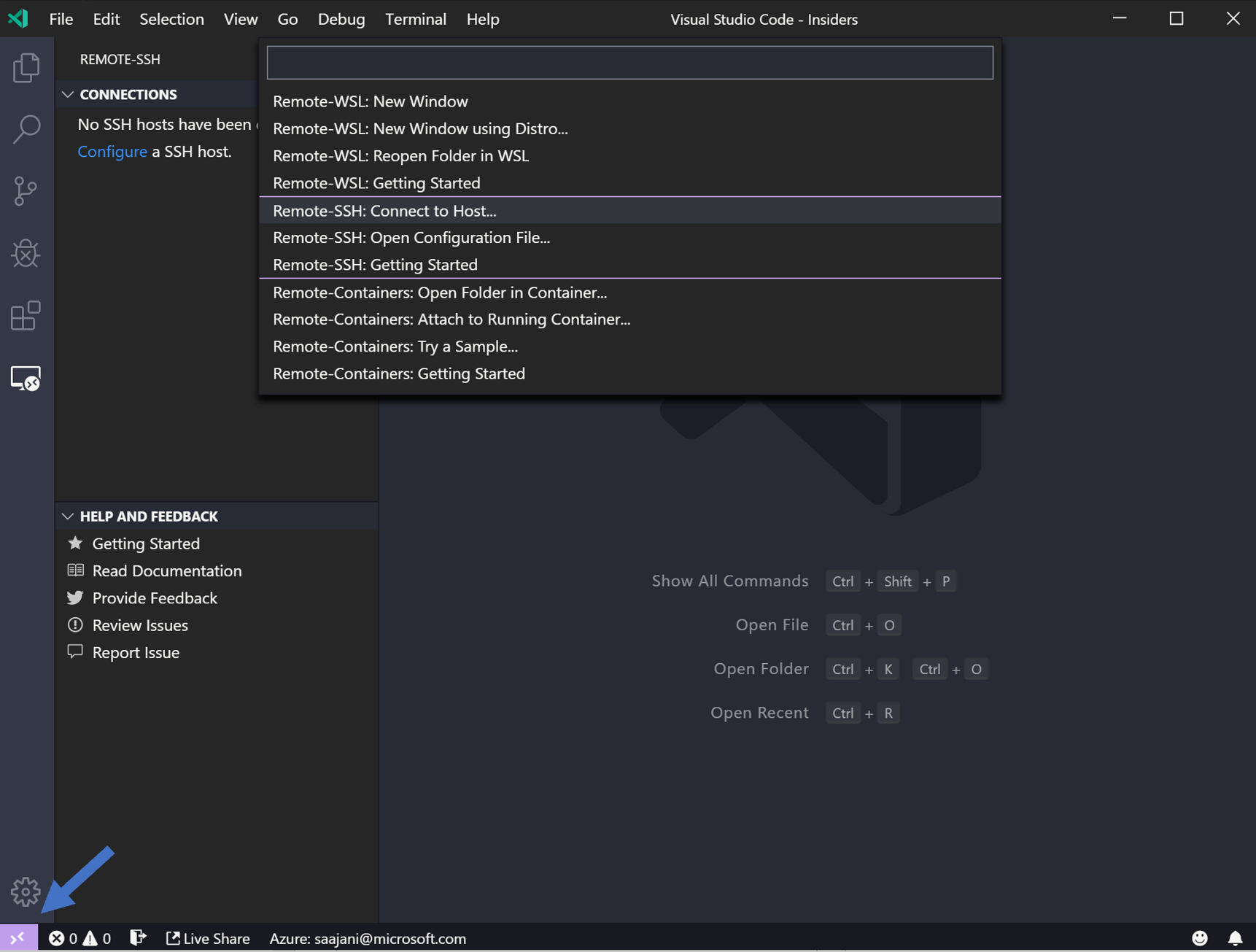
Visual studio code remote ssh public key prizesno