Exploring Real-World IoT SSH Applications Examples For Enhanced Connectivity
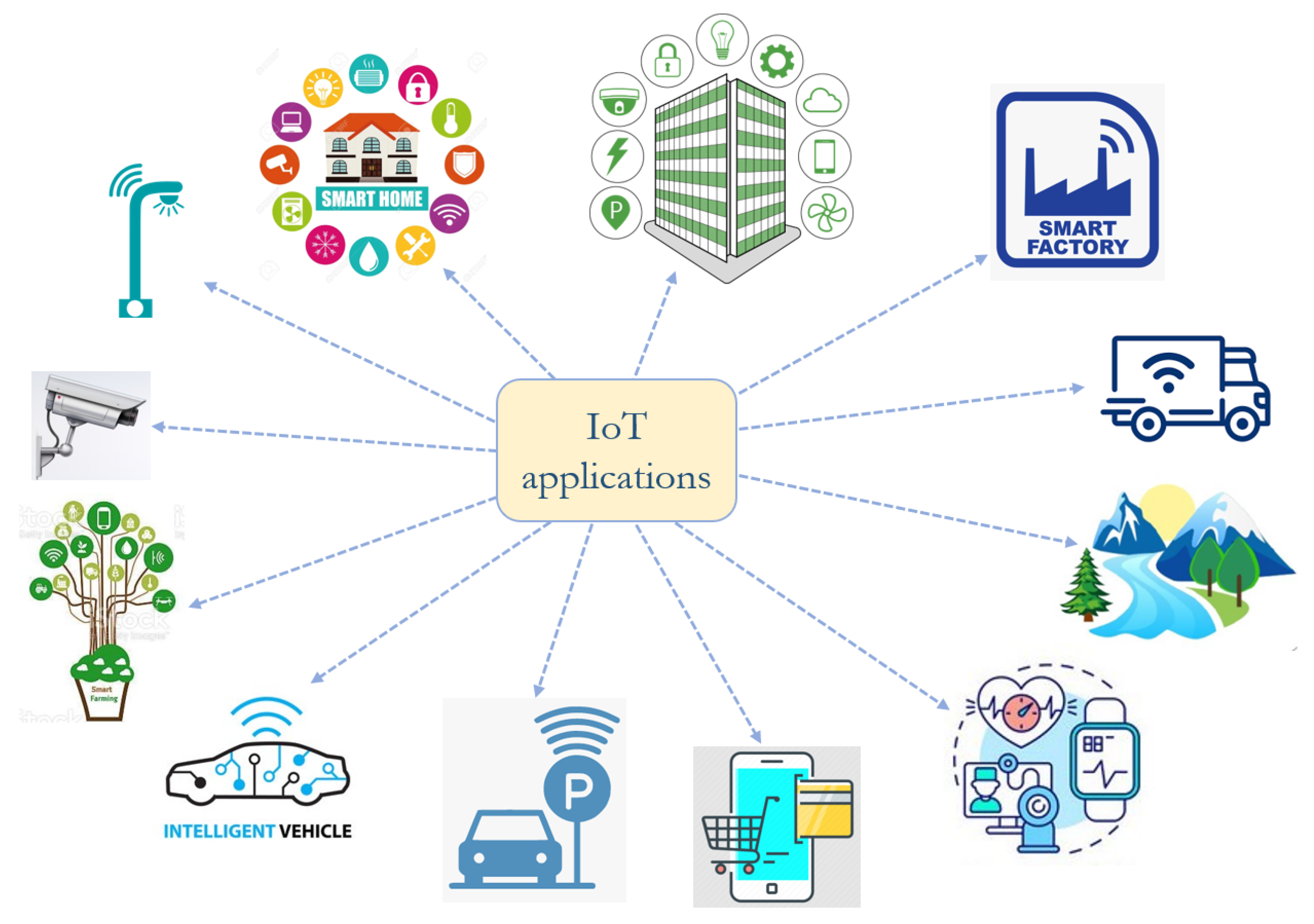
IoT SSH applications examples are revolutionizing the way devices communicate securely over networks. Secure Shell (SSH) has become a cornerstone for managing and securing IoT devices, enabling seamless remote access and control. From smart homes to industrial automation, SSH ensures encrypted communication, protecting sensitive data from unauthorized access. As IoT ecosystems expand, understanding how SSH integrates into these systems is crucial for developers, engineers, and tech enthusiasts alike.
With the growing adoption of IoT, SSH applications examples are becoming more diverse and sophisticated. From managing remote sensors in agricultural fields to securing medical devices in healthcare, SSH provides a robust framework for secure device management. These applications not only enhance operational efficiency but also ensure that data integrity is maintained across interconnected devices. The versatility of SSH in IoT environments makes it a vital tool for modern-day connectivity.
For businesses and individuals alike, leveraging IoT SSH applications examples can lead to improved security and streamlined operations. Whether it’s automating tasks in a smart factory or remotely troubleshooting devices in a smart city infrastructure, SSH serves as the backbone of secure communication. This article delves into the various use cases of SSH in IoT, offering insights into how these applications are shaping the future of technology.
Read also:Matt Leblanc And Marina Pearl Leblanc A Deep Dive Into Their Lives And Legacy
Table of Contents
- What Are IoT SSH Applications Examples?
- How Does SSH Enhance IoT Security?
- Examples of IoT SSH Applications in Smart Homes
- Can SSH Be Used for Industrial Automation?
- IoT SSH Applications Examples in Healthcare
- Why Is SSH Critical for Remote Device Management?
- How to Implement SSH in IoT Systems?
- IoT SSH Applications Examples for Smart Cities
- What Are the Challenges of Using SSH in IoT?
- Future Trends in IoT SSH Applications Examples
What Are IoT SSH Applications Examples?
IoT SSH applications examples refer to the practical use of Secure Shell (SSH) protocols in managing and securing Internet of Things (IoT) devices. SSH provides a secure channel over an unsecured network, enabling encrypted data transmission and authentication. This is particularly important in IoT environments, where devices often operate in untrusted or public networks.
Common IoT SSH applications examples include remote device management, secure firmware updates, and encrypted data transfer. For instance, SSH can be used to remotely access a smart thermostat to adjust settings or troubleshoot issues without exposing sensitive data to potential attackers. Similarly, in industrial IoT (IIoT), SSH ensures secure communication between sensors and control systems, preventing unauthorized access or tampering.
By leveraging IoT SSH applications examples, organizations can enhance the security and reliability of their IoT ecosystems. These applications not only protect data but also improve operational efficiency by enabling seamless remote management of devices.
How Does SSH Enhance IoT Security?
SSH plays a pivotal role in enhancing IoT security by providing robust encryption and authentication mechanisms. In IoT ecosystems, devices often exchange sensitive data, such as personal information or operational commands. Without proper security measures, this data can be intercepted or manipulated by malicious actors.
One of the key benefits of SSH is its ability to encrypt data in transit. This ensures that even if data is intercepted, it cannot be read or altered without the decryption key. Additionally, SSH uses public-key cryptography for authentication, making it difficult for unauthorized users to gain access to IoT devices.
By integrating IoT SSH applications examples into their systems, organizations can mitigate risks such as data breaches, unauthorized access, and device tampering. This is particularly important in industries like healthcare and finance, where the stakes are high, and the consequences of security lapses can be severe.
Read also:Discovering Zoe Perry And Her Father A Journey Into Family Talent And Legacy
Examples of IoT SSH Applications in Smart Homes
Smart homes are one of the most prominent examples of IoT SSH applications examples in action. These environments rely on interconnected devices, such as smart locks, thermostats, and security cameras, to enhance convenience and safety. However, the increased connectivity also introduces security risks, which SSH helps mitigate.
For instance, SSH can be used to securely access and manage smart locks, ensuring that only authorized users can control them remotely. Similarly, SSH enables encrypted communication between smart thermostats and mobile apps, protecting sensitive data such as temperature settings and usage patterns.
Another example is the use of SSH in smart home security systems. By encrypting data transmitted between cameras and monitoring devices, SSH prevents unauthorized access to live feeds or recorded footage. These IoT SSH applications examples highlight the importance of SSH in maintaining the security and privacy of smart home ecosystems.
Can SSH Be Used for Industrial Automation?
Industrial automation is another domain where IoT SSH applications examples are making a significant impact. In industrial IoT (IIoT) environments, devices such as sensors, actuators, and control systems work together to optimize production processes. However, these devices are often deployed in remote or unsecured locations, making them vulnerable to cyber threats.
SSH provides a secure way to manage and monitor these devices remotely. For example, engineers can use SSH to access control systems in a manufacturing plant, troubleshoot issues, and perform maintenance tasks without physically being present. This not only saves time but also reduces operational costs.
Moreover, IoT SSH applications examples in industrial automation ensure that sensitive data, such as production metrics and machine performance, is protected from unauthorized access. By leveraging SSH, organizations can enhance the security and efficiency of their industrial IoT ecosystems.
IoT SSH Applications Examples in Healthcare
The healthcare industry is increasingly adopting IoT technologies to improve patient care and operational efficiency. However, the sensitive nature of healthcare data makes security a top priority. IoT SSH applications examples play a crucial role in ensuring the secure transmission of medical data and the remote management of medical devices.
For instance, SSH can be used to securely access and manage remote patient monitoring devices, such as wearable sensors and smart implants. This enables healthcare providers to monitor patients' vital signs in real-time without compromising their privacy. Similarly, SSH ensures that data transmitted between medical devices and electronic health records (EHR) systems is encrypted and protected from unauthorized access.
Another example is the use of SSH in telemedicine applications. By encrypting communication between healthcare providers and patients, SSH helps maintain the confidentiality and integrity of medical consultations. These IoT SSH applications examples demonstrate how SSH enhances the security and reliability of healthcare IoT systems.
Why Is SSH Critical for Remote Device Management?
Remote device management is a key aspect of IoT ecosystems, and SSH is critical for ensuring secure and efficient management. In many IoT applications, devices are deployed in remote or inaccessible locations, making physical access impractical. SSH provides a secure way to manage these devices remotely, enabling tasks such as configuration updates, troubleshooting, and performance monitoring.
One of the main advantages of using SSH for remote device management is its ability to provide encrypted communication. This ensures that sensitive data, such as device configurations and operational commands, is protected from interception or tampering. Additionally, SSH's authentication mechanisms prevent unauthorized users from gaining access to devices.
IoT SSH applications examples in remote device management include managing smart meters in utility networks, monitoring environmental sensors in agricultural fields, and controlling drones in logistics operations. By leveraging SSH, organizations can enhance the security and efficiency of their remote device management processes.
How to Implement SSH in IoT Systems?
Implementing SSH in IoT systems requires careful planning and execution to ensure security and functionality. The first step is to choose the right SSH protocol version, as older versions may have vulnerabilities that can be exploited by attackers. SSH version 2 is recommended for its enhanced security features.
Next, organizations should configure SSH to use strong encryption algorithms and authentication methods. This includes using public-key cryptography for authentication and disabling password-based login to prevent brute-force attacks. Additionally, it's important to regularly update SSH software to patch known vulnerabilities and ensure compatibility with IoT devices.
Finally, organizations should monitor and audit SSH usage in their IoT systems to detect and respond to potential security incidents. This includes logging SSH sessions, analyzing access patterns, and enforcing access controls. By following these best practices, organizations can successfully implement IoT SSH applications examples and enhance the security of their IoT ecosystems.
IoT SSH Applications Examples for Smart Cities
Smart cities rely on IoT technologies to improve urban living, from traffic management to waste collection. However, the interconnected nature of these systems introduces security challenges that IoT SSH applications examples can address. SSH ensures secure communication between devices, protecting sensitive data and enabling efficient city operations.
For example, SSH can be used to securely manage traffic lights and sensors in a smart city's transportation network. This enables real-time monitoring and adjustment of traffic flow, reducing congestion and improving safety. Similarly, SSH ensures that data transmitted between waste management sensors and collection systems is encrypted, preventing unauthorized access.
Another example is the use of SSH in smart city surveillance systems. By encrypting communication between cameras and monitoring stations, SSH helps maintain the privacy and security of citizens. These IoT SSH applications examples demonstrate how SSH enhances the security and efficiency of smart city infrastructure.
What Are the Challenges of Using SSH in IoT?
While IoT SSH applications examples offer numerous benefits, there are also challenges associated with using SSH in IoT environments. One of the main challenges is the limited computational resources of many IoT devices, which can make it difficult to implement SSH protocols effectively.
Another challenge is the complexity of managing SSH keys across a large number of devices. In IoT ecosystems, devices are often deployed in large-scale networks, making it challenging to track and update SSH keys. This can lead to security vulnerabilities if keys are not properly managed.
Finally, ensuring compatibility between SSH software and IoT devices can be a challenge, particularly in heterogeneous environments where devices from different manufacturers are used. Organizations must carefully evaluate their IoT ecosystems and implement best practices to overcome these challenges and leverage the full potential of IoT SSH applications examples.
Future Trends in IoT SSH Applications Examples
The future of IoT SSH applications examples is promising, with emerging trends set to enhance their capabilities and adoption. One trend is the integration of artificial intelligence (AI) with SSH to enable predictive maintenance and anomaly detection in IoT systems. This can help organizations identify and address potential security threats before they escalate.
Another trend is the development of lightweight SSH protocols specifically designed for resource-constrained IoT devices. These protocols aim to provide the same level of security as traditional SSH while minimizing computational overhead. This will enable more IoT devices to benefit from SSH's secure communication capabilities.
Finally, the growing adoption of edge computing in IoT ecosystems is expected to drive the use of SSH for securing edge devices. By encrypting data at the edge, organizations can reduce latency and improve the overall security of their IoT systems. These trends highlight the evolving role of IoT SSH applications examples in shaping the future of secure connectivity.
Regan Kay Net Worth: Unveiling The Success Story Of A Rising Star
Kymberly Kalil Age: Everything You Need To Know About Her Life And Career
Zack Addy Bones: A Deep Dive Into The Life Of A Brilliant Forensic Scientist
Top 10 IoT Examples You Should Be Aware Of Realtime!, 59 OFF

10 Best Examples of IoT applications (2019)