AWS IoT Core SSH: Unlocking Secure Connections For IoT Devices
Secure communication between devices and servers is a critical component of modern IoT ecosystems, and AWS IoT Core SSH plays a pivotal role in enabling this. With AWS IoT Core, developers can seamlessly manage and connect IoT devices to the cloud, ensuring secure and reliable data transmission. By integrating SSH (Secure Shell) protocols, AWS IoT Core enhances the security of these connections, safeguarding sensitive data from potential threats. As businesses increasingly rely on IoT solutions, understanding how AWS IoT Core SSH works becomes essential for building robust and scalable systems.
IoT devices are deployed in various environments, from smart homes to industrial automation, where maintaining secure access is paramount. AWS IoT Core SSH allows administrators and developers to establish encrypted communication channels, ensuring that only authorized users and devices can interact with the system. This not only protects sensitive data but also minimizes the risk of unauthorized access or cyberattacks. With the growing adoption of cloud-based IoT platforms, AWS IoT Core SSH offers a reliable solution for managing secure device connections.
For organizations leveraging AWS IoT Core, integrating SSH capabilities provides an added layer of security and control. Whether you're managing a fleet of IoT devices or developing applications that require secure communication, AWS IoT Core SSH simplifies the process. By combining AWS's scalable infrastructure with the robust encryption of SSH, businesses can focus on innovation while ensuring their IoT ecosystems remain secure and efficient.
Read also:Exploring The Bold And Unforgettable Iconic Lady Gaga Outfits
Table of Contents
- What is AWS IoT Core SSH?
- How Does AWS IoT Core SSH Work?
- Why Use AWS IoT Core SSH for Secure Connections?
- How Can AWS IoT Core SSH Enhance Your IoT Projects?
- What Are the Benefits of Using AWS IoT Core SSH?
- How to Set Up AWS IoT Core SSH?
- Is AWS IoT Core SSH Suitable for Large-Scale Deployments?
- Common Challenges with AWS IoT Core SSH
- Best Practices for Using AWS IoT Core SSH
- Conclusion
What is AWS IoT Core SSH?
AWS IoT Core SSH refers to the integration of Secure Shell (SSH) protocols within the AWS IoT Core platform, enabling secure communication between IoT devices and cloud infrastructure. This combination allows developers to manage device connections, execute commands remotely, and ensure data integrity. AWS IoT Core SSH is particularly useful for organizations that require secure access to their IoT devices for maintenance, updates, or monitoring.
SSH is a cryptographic network protocol that provides secure communication over unsecured networks. When integrated with AWS IoT Core, SSH ensures that all interactions between devices and the cloud are encrypted, preventing unauthorized access or data breaches. This makes AWS IoT Core SSH an ideal solution for industries like healthcare, manufacturing, and logistics, where secure IoT communication is critical.
How Does AWS IoT Core SSH Work?
Understanding the inner workings of AWS IoT Core SSH is essential for leveraging its full potential. The process begins with device authentication, where each IoT device is registered with AWS IoT Core. Once authenticated, the device establishes a secure connection using SSH protocols. This connection is encrypted, ensuring that all data transmitted between the device and the cloud remains confidential.
AWS IoT Core SSH uses public-key cryptography to authenticate devices and users. This involves generating a pair of cryptographic keys: a public key, which is shared with AWS IoT Core, and a private key, which is securely stored on the device. When a connection is initiated, AWS IoT Core verifies the device's identity using the public key, ensuring that only authorized devices can access the system.
Why Use AWS IoT Core SSH for Secure Connections?
Security is a top priority for any IoT deployment, and AWS IoT Core SSH offers several advantages in this regard. First, it provides end-to-end encryption, ensuring that data cannot be intercepted or tampered with during transmission. Second, it supports multi-factor authentication, adding an extra layer of security to device connections.
Additionally, AWS IoT Core SSH simplifies the management of IoT devices by enabling remote access and control. Administrators can securely execute commands, update firmware, or troubleshoot issues without physically accessing the devices. This not only improves operational efficiency but also reduces downtime and maintenance costs.
Read also:Liam Neesons Children A Glimpse Into Their Lives And Legacy
How Can AWS IoT Core SSH Enhance Your IoT Projects?
Integrating AWS IoT Core SSH into your IoT projects can significantly enhance their security and scalability. By leveraging AWS's robust infrastructure, you can ensure that your devices remain connected and operational, even in challenging environments. AWS IoT Core SSH also supports real-time data processing, enabling you to make informed decisions based on accurate and timely information.
For example, in a smart agriculture project, AWS IoT Core SSH can securely transmit data from sensors monitoring soil moisture, temperature, and humidity to the cloud. This data can then be analyzed to optimize irrigation schedules and improve crop yields. By using AWS IoT Core SSH, you can ensure that this data remains secure and accessible only to authorized users.
What Are the Benefits of Using AWS IoT Core SSH?
There are several benefits to using AWS IoT Core SSH for your IoT deployments. First, it provides a high level of security, protecting your devices and data from cyber threats. Second, it simplifies device management by enabling remote access and control. Third, it integrates seamlessly with other AWS services, allowing you to build comprehensive IoT solutions.
Other benefits include scalability, reliability, and cost-effectiveness. AWS IoT Core SSH can handle large-scale deployments, ensuring that your IoT ecosystem remains operational as it grows. It also offers built-in redundancy and failover mechanisms, minimizing downtime and ensuring continuous connectivity.
How to Set Up AWS IoT Core SSH?
Setting up AWS IoT Core SSH involves several steps, starting with device registration. Each IoT device must be registered with AWS IoT Core and assigned a unique identity. This identity is used to authenticate the device and establish a secure connection using SSH protocols.
Here’s a step-by-step guide to setting up AWS IoT Core SSH:
- Register your IoT device with AWS IoT Core.
- Generate a pair of cryptographic keys (public and private).
- Upload the public key to AWS IoT Core.
- Store the private key securely on the device.
- Configure the device to use SSH for secure communication.
- Test the connection to ensure it is working correctly.
Is AWS IoT Core SSH Suitable for Large-Scale Deployments?
Yes, AWS IoT Core SSH is highly suitable for large-scale deployments. AWS IoT Core is designed to handle millions of devices simultaneously, making it an ideal choice for enterprises with extensive IoT ecosystems. By integrating SSH protocols, AWS IoT Core ensures that all device connections remain secure, even as the number of devices grows.
For large-scale deployments, AWS IoT Core SSH offers features like automatic scaling, load balancing, and fault tolerance. These features ensure that your IoT ecosystem remains operational and secure, regardless of the number of devices or the volume of data being transmitted.
Common Challenges with AWS IoT Core SSH
While AWS IoT Core SSH offers numerous advantages, there are some challenges to consider. One common issue is managing cryptographic keys securely. If private keys are compromised, unauthorized users could gain access to your IoT devices, posing a significant security risk.
Other challenges include:
- Ensuring compatibility with legacy devices.
- Managing device identities and permissions.
- Monitoring and troubleshooting connections.
Best Practices for Using AWS IoT Core SSH
To maximize the benefits of AWS IoT Core SSH, it’s important to follow best practices. These include:
- Regularly rotating cryptographic keys to minimize the risk of compromise.
- Implementing multi-factor authentication for added security.
- Monitoring device activity to detect and respond to potential threats.
- Using AWS IoT Core's built-in tools for managing device identities and permissions.
Conclusion
AWS IoT Core SSH is a powerful tool for securing IoT device connections and ensuring reliable communication between devices and the cloud. By leveraging AWS's scalable infrastructure and the robust encryption of SSH, businesses can build secure and efficient IoT ecosystems. Whether you're managing a small fleet of devices or deploying a large-scale IoT solution, AWS IoT Core SSH offers the features and capabilities needed to succeed.
By following best practices and addressing common challenges, you can maximize the benefits of AWS IoT Core SSH and ensure that your IoT deployments remain secure and scalable. With its ability to integrate seamlessly with other AWS services, AWS IoT Core SSH is an essential component of any modern IoT strategy.
Diddy Audio: Unveiling The Legacy Of A Music Mogul
Dr Disrespect Wife: The Woman Behind The Controversial Streamer
Edward Ruttles Partner: Unveiling The Life And Legacy
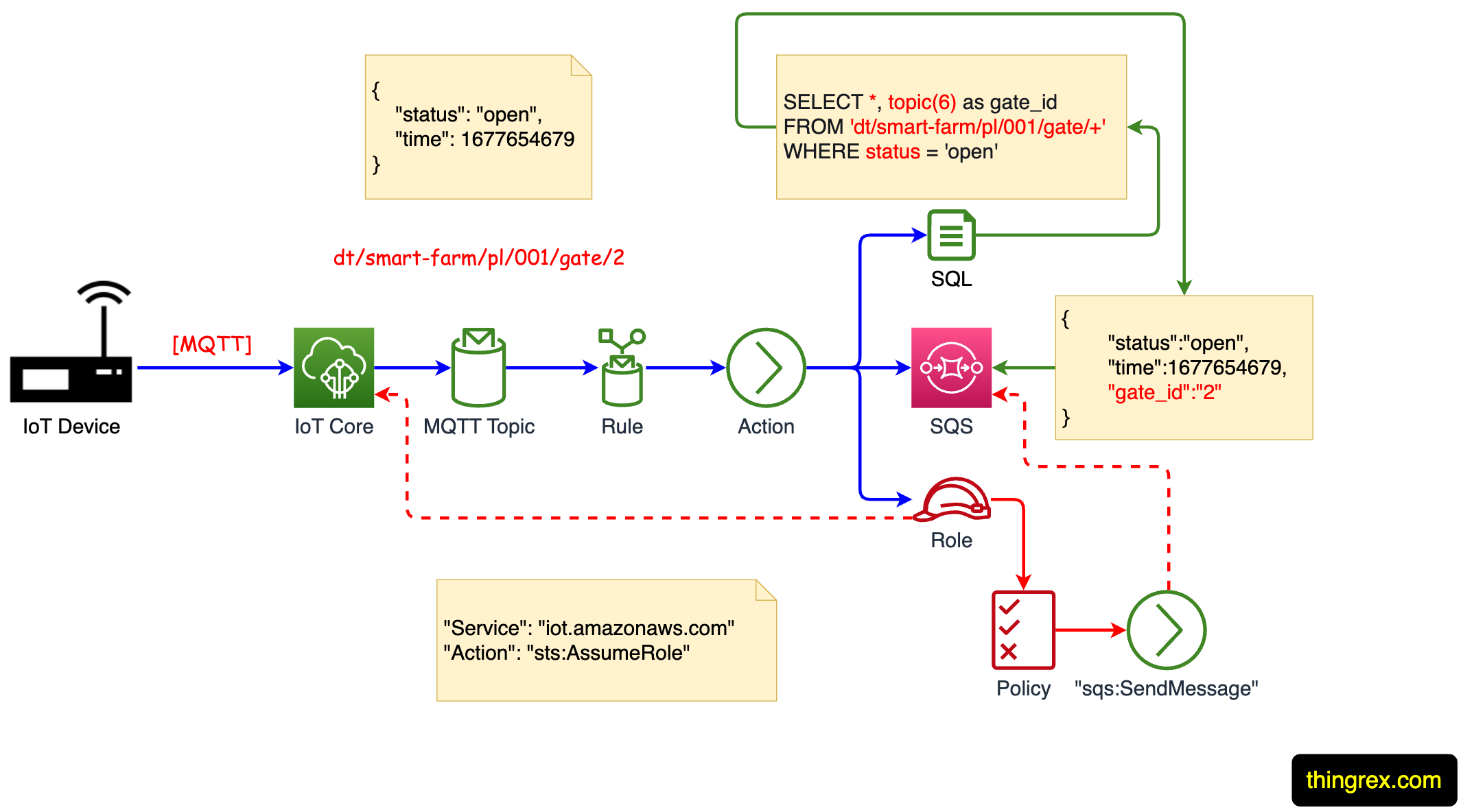
AWS IoT Rules Engine overview
AWS IoT Core Scaler Topics